By Edy Werder — IT Consultant & Tech Blogger
Hello, tech enthusiasts. Edy here. This guide covers setting up SSH keys on Synology from start to finish: enabling SSH in DSM, generating keys with PuTTYgen on Windows, and switching to key-based login for better security.
You’ll get a clear step-by-step walkthrough to connect safely and lock things down.

Setting up SSH keys on Synology is safer than password logins. Enable SSH in DSM web interface, generate a key pair with PuTTYgen on Windows, then add the public key to authorized_keys in your Synology user’s ~/.ssh folder. Test key-based login with the private key first. Only then disable password login and further lock SSH down.
- Test login, then restrict SSH to trusted IPs (firewall)
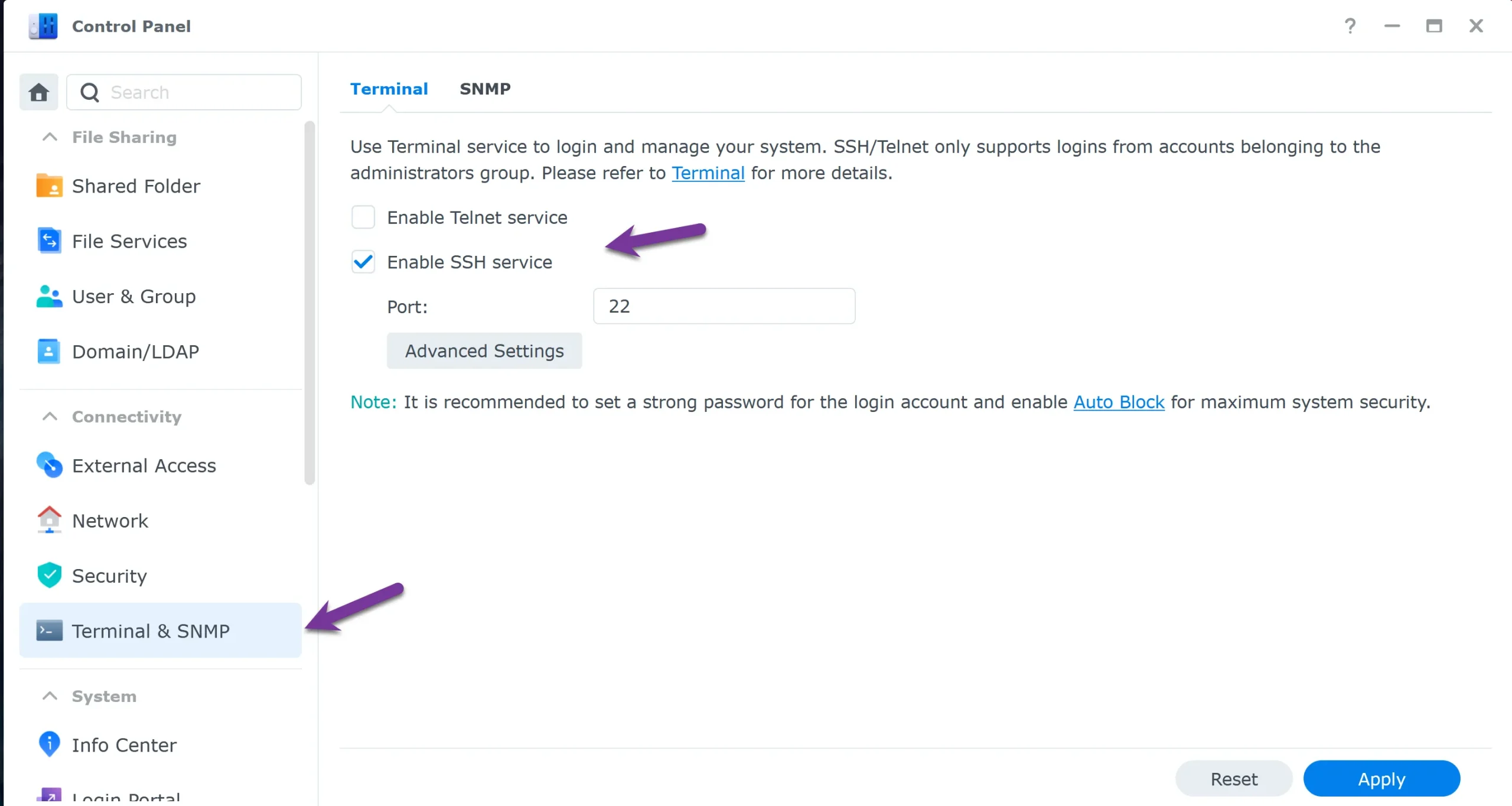
- Enable SSH: Control Panel → Terminal & SNMP → Enable SSH service
- Generate keys with PuTTYgen and save the private key (.ppk)
- Add the public key to: ~/.ssh/authorized_keys (one key per line)
- Fix permissions if needed: .ssh 700, authorized_keys 600
Part 1: Generating a Synology SSH Key with PuTTYgen
Securing your Synology NAS with SSH begins with creating a robust SSH key. I’ve always found PuTTYgen to be an excellent tool for this. Here’s my approach:
Step 1: Download and Open PuTTYgen:
- My first step in securing Synology SSH access is downloading PuTTY from https://www.putty.org/. After installation, I launch PuTTYgen, ready to start the critical generation process. Type “puttygen” in the Windows search box.
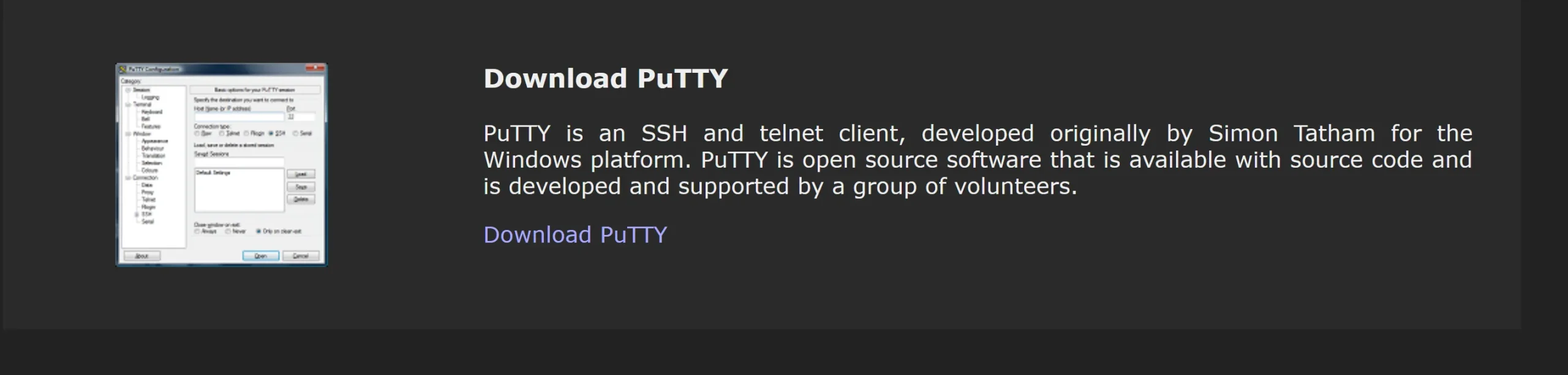
Step 2: Generate the Key pair:
- In PuTTYgen, I click “Generate” and move my mouse around to create randomness. This randomness is crucial for a secure Synology SSH key.
Optional Passphrase:
- I often add a passphrase for an extra layer of security. This step is vital for ensuring your Synology SSH access remains secure.
Step 3: Save the SSH config file:
- After generating the key, I save the private key file and store it in a secure store. Please don’t use the “Save public key” button to save the public key. Unfortunately, it will save the public key file in a format Synology cannot read. Instead, use the “public key” field and copy/paste the authorized_keys content to Notepad.

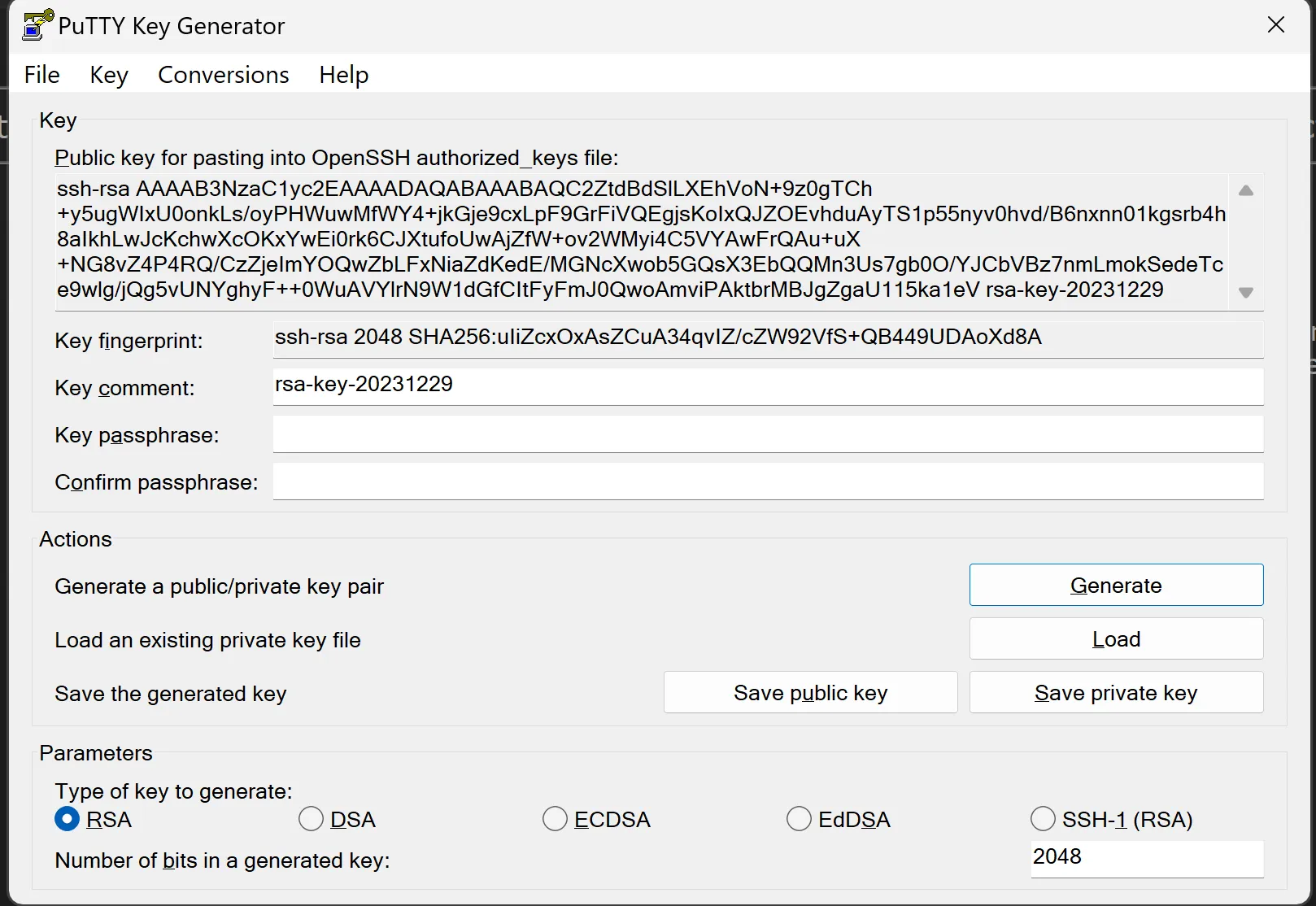
Ensure that the public key in the authorized_keys file is on a single line with no breaks. Sometimes, copying and pasting can insert line breaks that invalidate the key.
Below is an example the line should start with “ssh-rsa….”
Part 2: Applying the SSH Key for Synology SSH
With our SSH key ready, let’s apply it to the Synology NAS.
Step 4: Enable SSH service on Synology NAS:
- I enable SSH service in the DSM under Control Panel > Terminal & SNMP to secure my Synology SSH access.
Step 5: Adding the ssh directory (authorized keys) to Synology NAS:
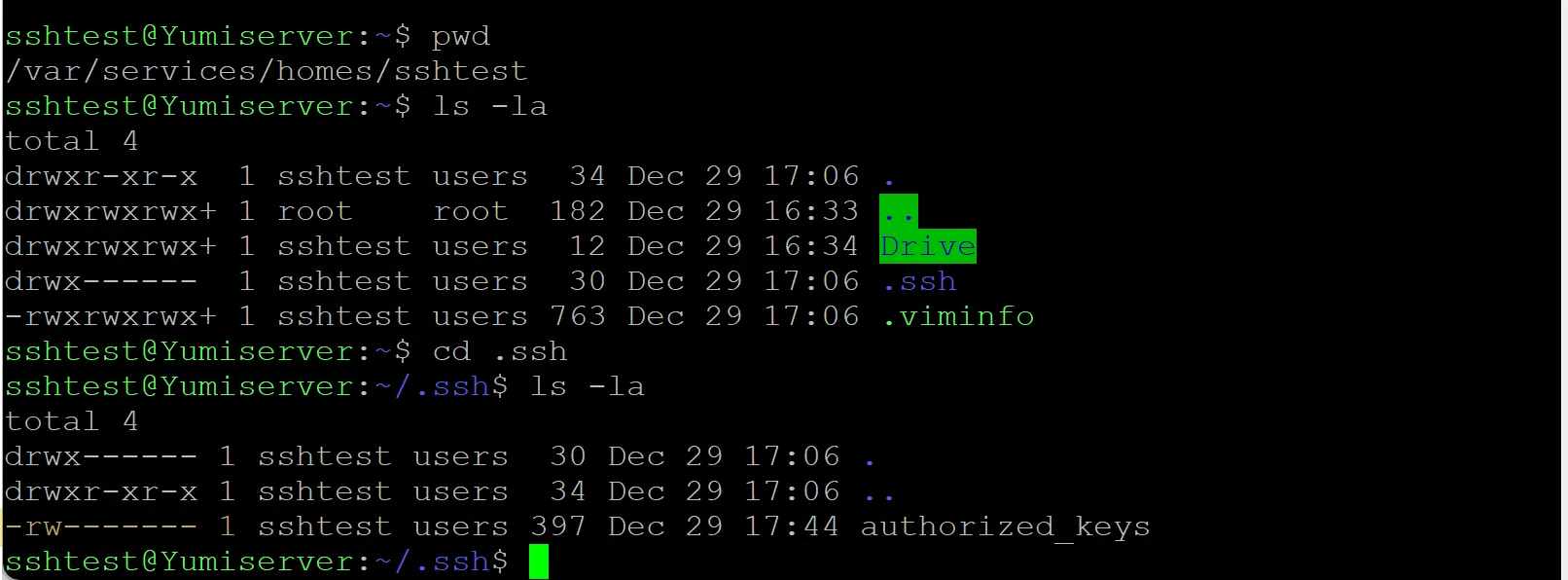
The file ~/.ssh/authorized_keys must be created on the Synology NAS to store the public key.
- Access File Station on Your Synology NAS:
- Navigate to Your Home Directory:
- Create the
.sshFolder: - Create the
authorized_keysFile:
Step 6: Setting Correct Permissions for Home Directories on Synology NAS:
To establish secure SSH access with authorized_keys on a Synology NAS, it’s crucial to adjust the permissions of user home directories. By default, Synology sets these directories to 777 permissions, which are overly permissive and can lead to SSH errors such as ‘server refused the key.’
For Individual User Home Directory:
- Connect to Your Synology NAS via SSH:
- Navigate to the Homes Directory:
- Change Permissions for a Specific User’s Home Directory:
For All User Home Directories:
- Understand the Implications:
- Bulk Change Command:
Additional Steps for .ssh and authorized_keys:
- Ensure the
.sshdirectory in each user’s home has700permissions (chmod 700 .ssh), and theauthorized_keysfile has600permissions (chmod 600 .ssh/authorized_keys).
In the screenshot below, you see the permission for the folder .ssh and for the file authorized_keys
I recommend my article “Linux file permissions explained: What you need to understand” for more information about Linux file and folder permissions. A good reference is the chmod calculator.
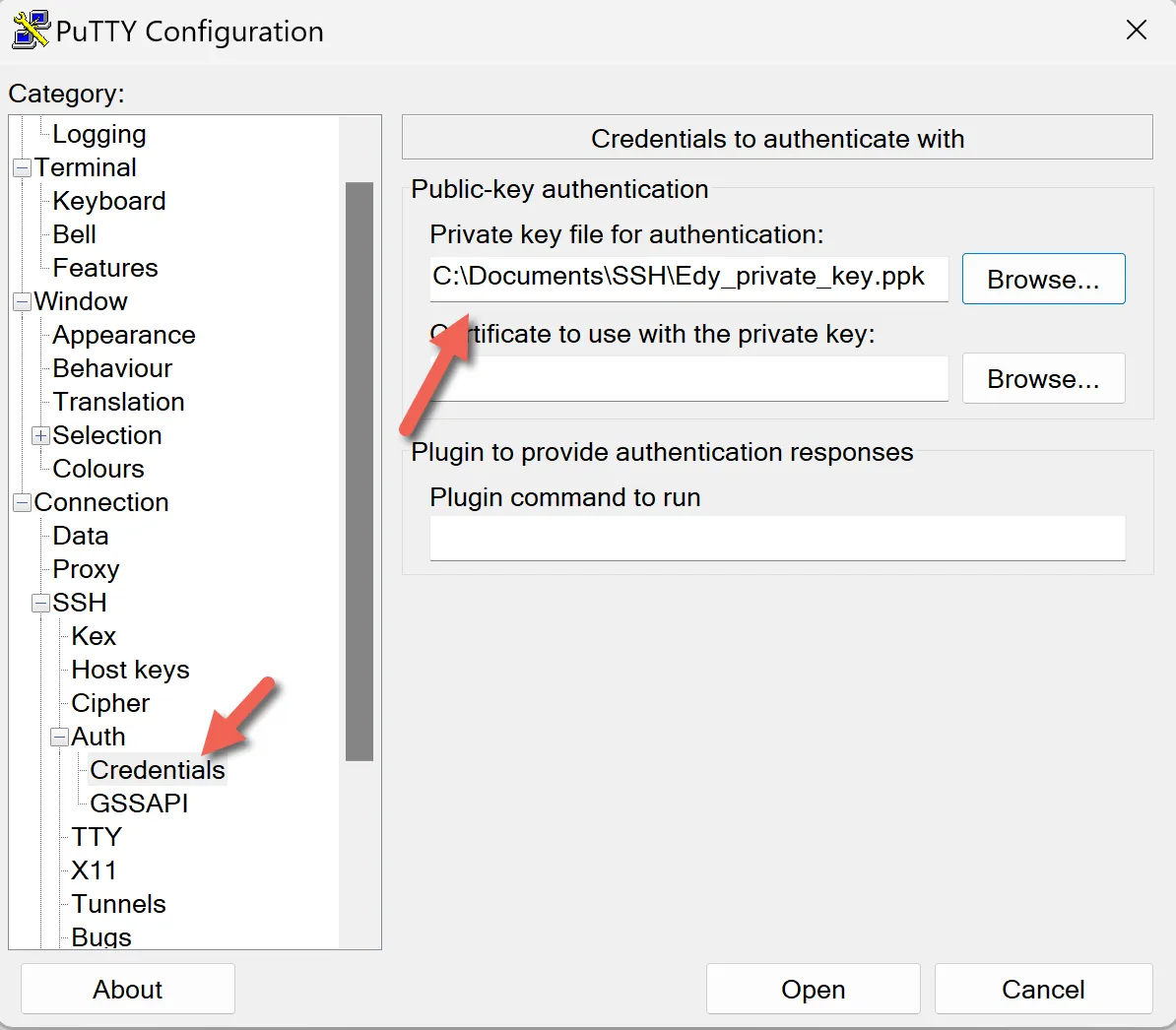
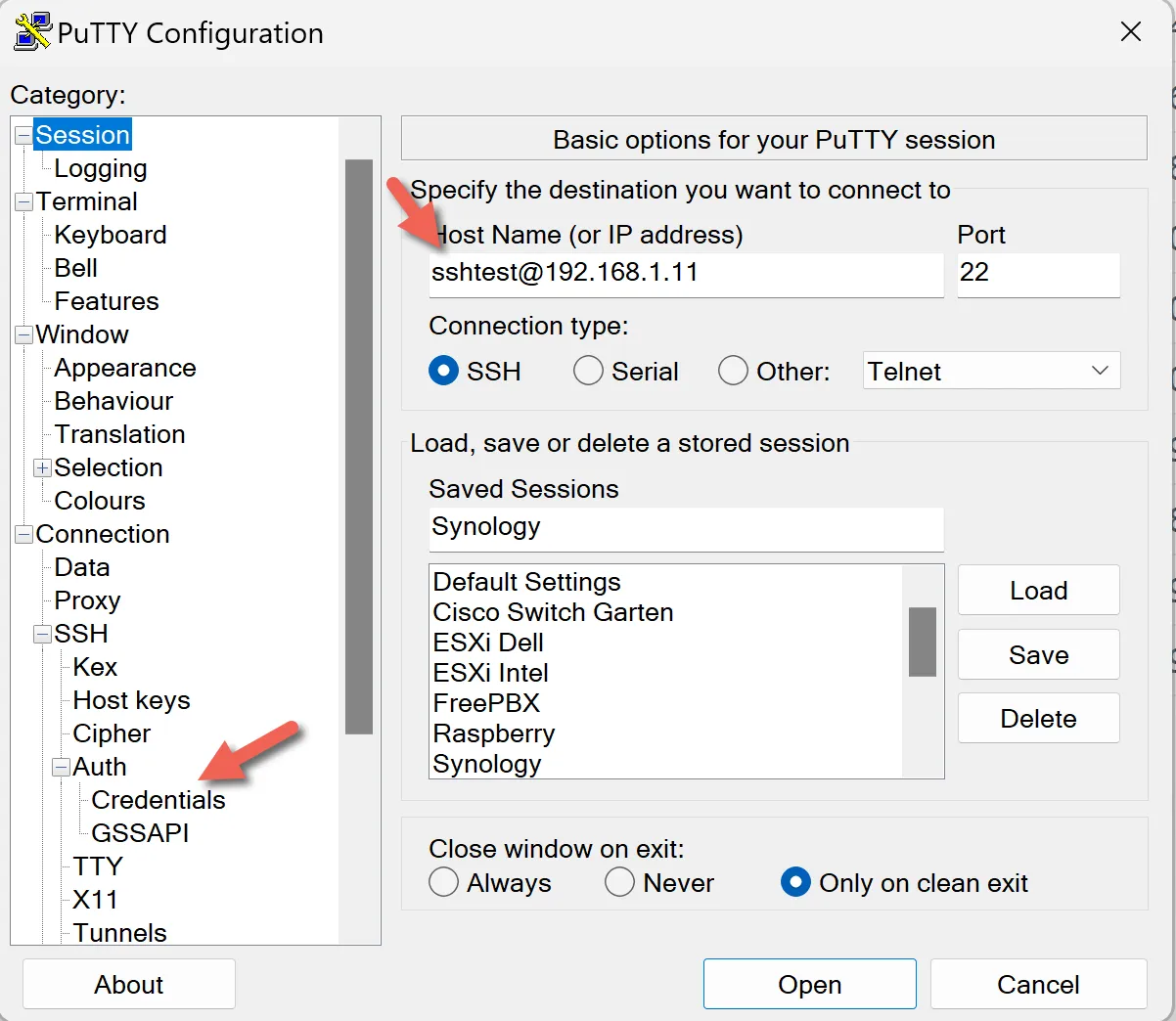
Last Step 7: Connecting via SSH:
- To test our Synology SSH access, I open PuTTY, enter my NAS’s IP address, and load my private key under Connection > SSH > Auth. After saving these settings, I click Open to connect.
FAQs on Synology SSH and Security:
Conclusion:
That’s it for setting up SSH keys on Synology with PuTTYgen. You now have SSH key authentication in place, which is a big security upgrade over passwords. If you want to harden things further, review your sshd_config, keep the sshd service running only when you need it, and restrict access in DSM Firewall to trusted IPs. Questions or edge cases? Drop them in the comments.
I’d love to hear from you — was this article helpful? Share your thoughts in the comments below. If you prefer, you can also reach me by email or connect with me on Reddit at Navigatetech.
Before you go …
If you found the guide on setting up SSH keys on Synology insightful, you might appreciate the next step: SSH into Synology. This article delves into securely accessing your Synology device via SSH, building on the knowledge you’ve gained about SSH key setup. It’s a practical read for enhancing your remote management skills and ensuring secure access to your Synology NAS. Perfect for tech enthusiasts aiming to streamline their network management tasks!
Related Articles
About the author
Hi, I’m Edy Werder. I write hands-on guides about Proxmox, homelab servers, NAS, and WordPress, based on real setups I run and document.
No sponsors, no fluff—just real configs and results.
Enjoying the content?