By Edy Werder — IT Consultant & Tech Blogger

Fortinet released FortiOS 6.2 for Fortigate firewalls in March 2019. See the official what’s new document from Fortinet. I would like to highlight some nice new settings in this blog.
Before I get into describing the new settings, first things first. Fortinet released a patch 6.2.1 on July 19, 2019 to fix a critical hole. What exactly was fixed is not known. Interestingly, even end of life FortiOS versions received the patch.
The screenshots used are from a Fortigate 60E with the UTM protection bundle. The bundle has more features like Web filtering, DNS filtering and Application Control.
Remember to always begin with a configuration backup. If you upgrade the firmware online from the WebGUI, Fortigate will create one for you. I liked the configuration file. It’s in easy to understand language and perfectly viewable in Notepad++. It is possible to make changes directly in the file and restore it. But important to note that a configuration file cannot be restored to another Fortigate model. For that you would need FortiConverter. This is a wonderful tool to convert your configuration to another model. It even converts configuration files from other firewall manufacturers. FortiConverter is available free for conversion within the Fortigate family. To convert configuration files from other manufacturers one needs to buy a license.
And now for a look at some of the nice new settings I mentioned earlier.
FortiView
A great new feature. almost all Sub-Menus let you drill-down to get more detailed information for the session by right clicking. And that’s not all. Various tabs like Sources or Destinations show more specific details. I found the policy tab to be useful, since it shows which firewall policy allowed the session.
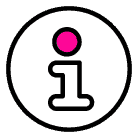
Automation
A very powerful way to schedule a CLI script for certain tasks. For example, you could schedule a daily backup of the firewall configuration. The FortiOS Event log is another new trigger. Here you can select a log event and get notified by email.
Fabric Connector
The Fabric Connector under Security Fabric now has more choices. By adding Vcenter or ESXi host(s) you are able to create objects from Vcenter under addresses. How cool is that! The address objects could also be used for firewall policy. VM networks objects are available too. This connector simplifies things because you don’t need to add objects manually with IP address.
Threat feeds,. in the same list, are new too. You could add IP abuse lists found on the internet. The list is refreshed periodically, with a default of 5 min. No need to create an object in addresses first. After that the IP addresses could also be used in a firewall policy. Simple enough, yet efficient.
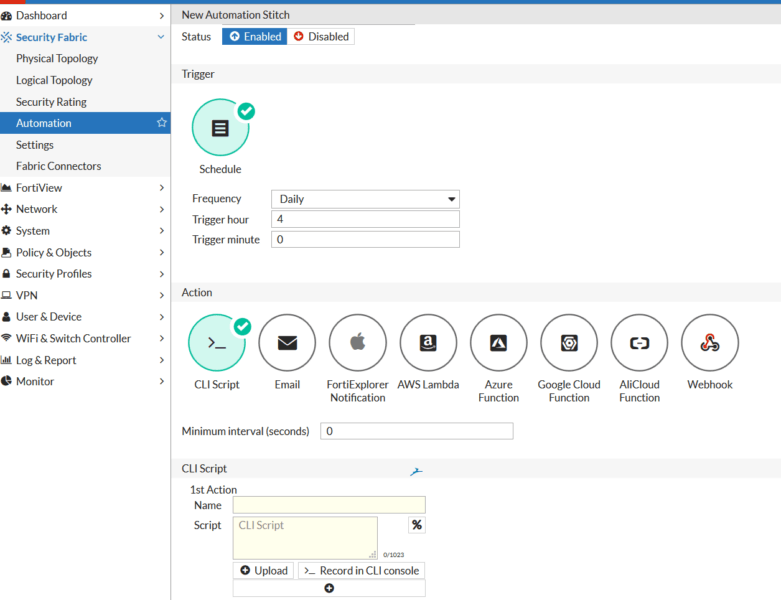
Reputation
Here I could query any IP address to check their reputation. Quickly obtain information for an IP. A very convenient new feature.
Internet Service Database
Fortigate added a new column called Reputation to rate different kinds of internet services. Numbered from 1 to 5, with 1 being malware services, 2 being Tor or peer to peer, 3 being neutral and 4 being social media. The good thing is, it is possible to use the data for a firewall policy. By the way every service which is not in the database has the reputation 3 which is neutral. For example grant only traffic to destination with minimum reputation of 3.
An example: Set reputation to 3 minimum and direction to destination
set reputation-minimum 3
set reputation-direction destination
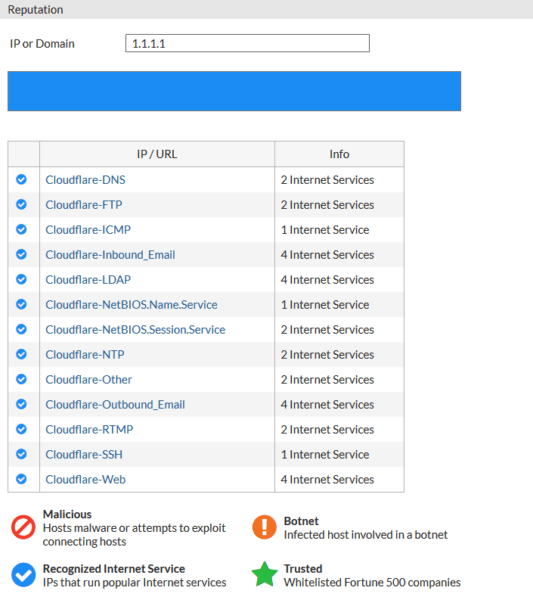
Unfortunately you cannot use the GUI to configure a firewall policy with reputation data. So you will need to use the CLI. Go to the policy you want to change in the GUI, right click and select “edit in CLI”. It’s the best way to reach the CLI and see how the policy has been configured so far.
What does this mean in practical terms? All outgoing connections to destination addresses with reputation below 3 will be blocked. Cool isn’t it? However, in the GUI the destination field remains blank. I hope Fortigate changes this in a future FortiOS release. also It will then become possible to configure reputation in the GUI.
Addresses
I would like to mention two new features. In the menu interface there is a new field called ”Create address object matching subnet”. This might be useful in certain scenarios. In menu addresses there is a new type called “device MAC address” with scope of single or range. I could well imagine that this would be great to create a device group and use in a firewall policy.
Some other new changes:
- Consolidated policy
Combine IPv4 and IPv6 firewall rule into one rule. Time saver if you are someone who uses both.
Activate the new mode in the CLI - Application control / Network Protocol Enforcement
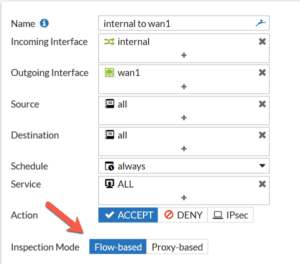
Make sure a port is used only for the specifically assigned service. For example, DNS traffic on port 53 should not be used for traffic other than DNS. - Inspection mode
New feature to configure inspection mode for each individual firewall policy.
flow based or proxy based. In earlier firmware the choice applied to the entire firewall. Could be helpful for some use case.
FortiClient
Fortinet changed its licensing policy. FortiClient is no longer free with endpoint security capability. A new application called FortiClient VPN is available now, which is a free version with VPN functionality only. It provides only IPSec VPN and SSL VPN. This should not be a problem, as most likely for endpoint security you would have another solution in place
I think FortiOS 6.2 has some nice new features that are not apparent at first glance. Sometimes you need to look closer to discover a new change. This article is more to describe some of the cool new features and not meant to be comprehensive.
About the author
Hi, I’m Edy Werder. I write hands-on guides about Proxmox, homelab servers, NAS, and WordPress, based on real setups I run and document.
No sponsors, no fluff—just real configs and results.
Enjoying the content?