By Edy Werder — IT Consultant & Tech Blogger
Have you ever wondered what NAT is and when to configure NAT on FortiGate firewalls? In this article, I want to explain what NAT is and when you need to configure it. Perhaps you have the same question as I did when starting with a Fortigate firewall. There is a toggle to turn NAT on for firewall policies, but when should I turn it on?
First, I would like to explain some basics about NAT to you.

What is NAT and Its Importance in FortiGate Firewall Configuration
Network Address Translation (NAT) is a fundamental concept in networking, especially when configuring a FortiGate Firewall. Essentially, NAT acts as a translator, converting the private IP addresses used within your local network into public IP addresses that can communicate over the internet.
Let’s break it down:
- What is NAT?: NAT is like a translator that converts IP addresses. In your network, devices like computers and phones use private IP addresses to communicate internally. When these devices need to access the internet, NAT translates these private IP addresses into public IP addresses recognized by the internet.
- Why is NAT Important for FortiGate?: FortiGate Firewalls use NAT to enhance security and manage network traffic efficiently. By translating IP addresses, FortiGate ensures that internal devices remain hidden from external threats while still being able to access online resources. This helps protect your network from unauthorized access and cyber-attacks.
In simple terms, NAT in FortiGate Firewall Configuration ensures your network stays safe and secure while allowing your devices to communicate effectively with the outside world. It’s an essential feature for beginners learning to set up and manage their FortiGate firewall.
What is the difference between static NAT and source NAT?
Static NAT and Source NAT are two distinct types of Network Address Translation (NAT) techniques used in networking to manage the translation of IP addresses between private and public networks. Here’s an overview of each:
Static NAT (Network Address Translation):
Static NAT, also known as one-to-one NAT, involves mapping a specific private IP address to a corresponding public IP address on a one-to-one basis. In other words, it establishes a fixed relationship between an internal IP address and an external IP address. Static NAT is typically used when an internal device, such as a server or a network appliance, needs to be accessible from external networks.
Critical features of Static NAT include:
- Permanent Mapping: The mapping between the internal and external IP addresses remains constant and does not change over time.
- Inbound Access: Static NAT enables external users to access specific internal resources, such as web servers, email servers, or FTP servers, by providing a public IP address for communication.
- Security: By exposing only specific internal resources to the external network, Static NAT enhances security by limiting the exposure of internal network infrastructure.
Source NAT (Network Address Translation):
Source NAT (snat), also known as outbound NAT or PAT (Port Address Translation), involves translating the source IP address of outgoing packets from private IP addresses to a single public IP address before they leave the network. Unlike Static NAT, which focuses on inbound traffic, Source NAT primarily deals with outgoing traffic initiated by devices within the internal network.
Key features of Source NAT include:
- Dynamic Address Translation: Source NAT dynamically assigns public IP addresses to outgoing packets on a per-connection basis. This allows multiple internal devices to share a single public IP address.
- Internet Connectivity: Source NAT enables devices within the internal network to communicate with external servers and services over the internet by presenting a consistent public IP address for outbound connections.
- Port Multiplexing: In addition to translating IP addresses, Source NAT also performs port multiplexing, which maps multiple internal port numbers to unique port numbers on the public IP address, allowing simultaneous connections from multiple internal devices.
In summary, Static NAT is used for inbound access to specific internal resources, while Source NAT is used for outbound traffic from internal devices to the internet. Both techniques are crucial in managing network communication and ensuring secure and efficient data transfer between private and public networks.
Do you need NAT for internal traffic to VLAN?
Network Address Translation (NAT) is typically not required for internal traffic between VLANs when each VLAN is assigned a different subnet. NAT is primarily used for translating IP addresses between private and public networks or between different address realms within the same network.
When VLANs are assigned different subnets, each VLAN operates within its own IP address space. Traffic between devices within the same VLAN can communicate directly without needing address translation, as they share the same subnet and can route traffic based on their subnet masks.
Similarly, when traffic needs to traverse between VLANs with different subnets within the same internal network, routers or Layer 3 switches handle the routing process. These devices use routing tables to determine the appropriate path for forwarding traffic between VLANs based on their IP addresses and subnet configurations.
How can you configure NAT on FortiGate Firewall?
Configuring NAT on the FortiGate Firewall is pretty straightforward. There are several ways, the most common of which is through a firewall policy.
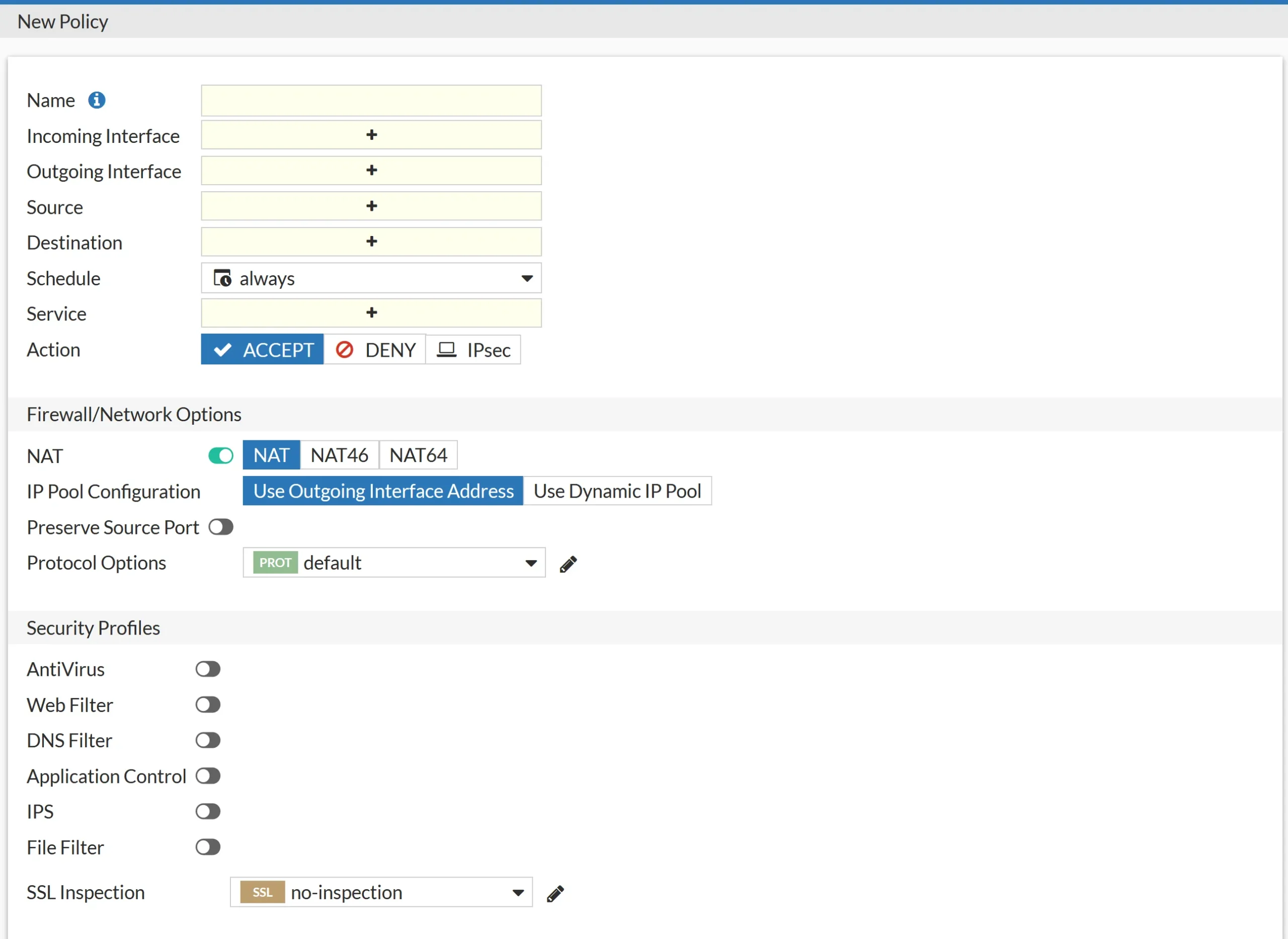
Creating Source NAT Policies for Outgoing Traffic
- Navigate to the “Policy & Objects” tab and select “Firewall Policy”.
- Click on “Create New” to define a new policy.
- Specify the incoming and outgoing interfaces, source and destination addresses, services, and action for the outgoing traffic.
- Under the “NAT” section, enable NAT and select “NAT”
- IP Pool Configuration: Choose the outgoing interface address or a dynamic IP pool.
- Save the policy and apply the changes.
NAT46
NAT46 allows for the translation of IPv4 addresses to IPv6 addresses and vice versa. It enables communication between IPv4-only and IPv6-only networks by performing address translation at the network.
NAT64
NAT64 performs the translation of IPv6 addresses to IPv4 addresses and vice versa. It enables communication between IPv6-only and IPv4-only networks by facilitating address translation between the two protocols.
Another way to configure Nat on Fortigate Firewall is virtual IPs. or IP pools.
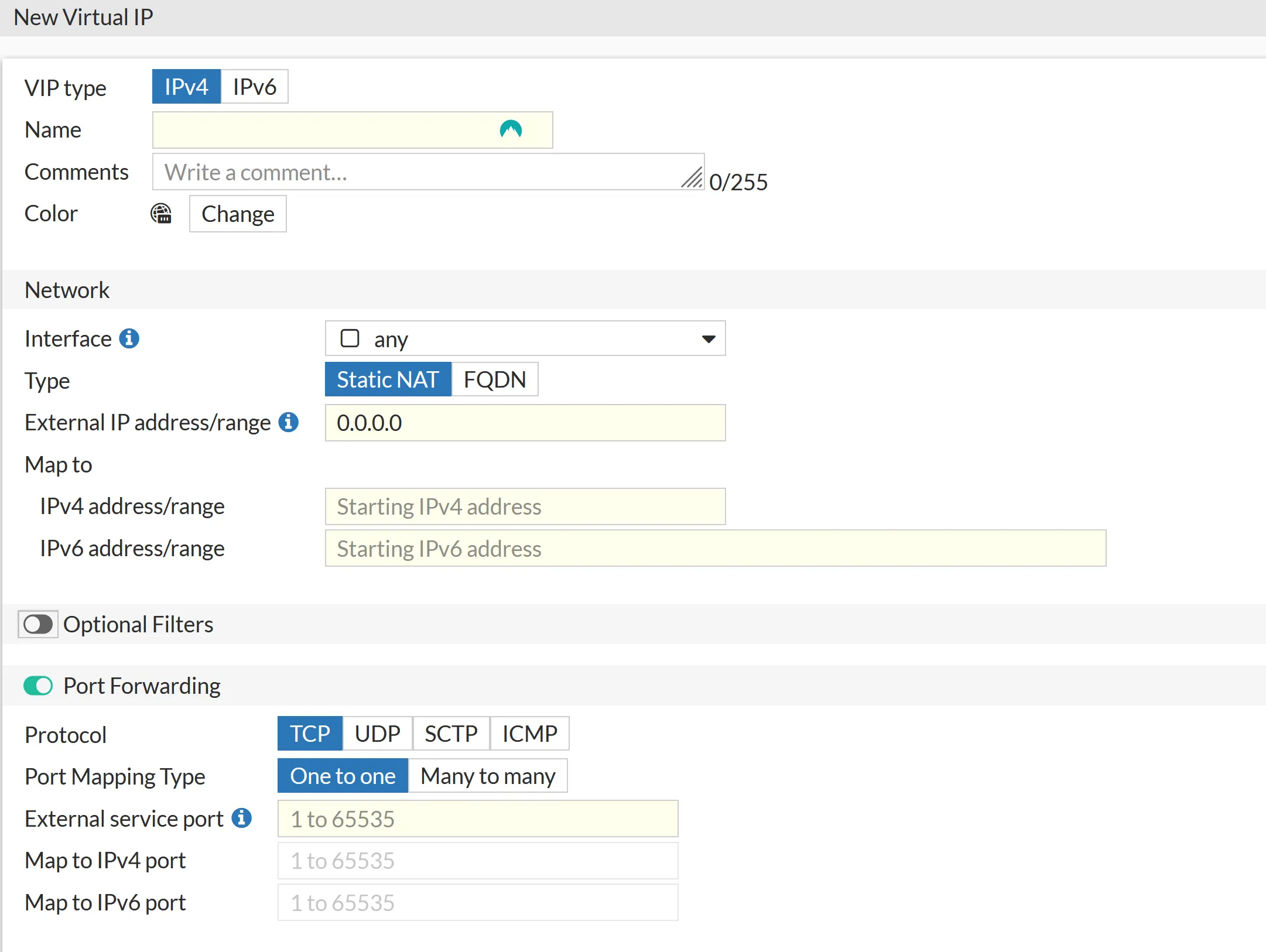
Virtual IPs
Virtual IPs (VIPs) or port forwarding is a form of Network Address Translation (NAT).
In the context of FortiGate firewalls, Virtual IPs allow you to map external IP addresses and ports to internal servers or services. This mapping enables incoming traffic destined for a specific external IP address and port to be forwarded to a corresponding internal IP address and port.
This process involves translating the destination IP address and port of incoming packets from the external IP address to the internal IP address, allowing external users to access internal resources hosted behind the firewall.
Virtual IPs are typically used to forward ports like 80,443,21 and so on to an internal server.
featured blog

Best Homelab Firewall
Hardware and Software to Keep Your Network Secure
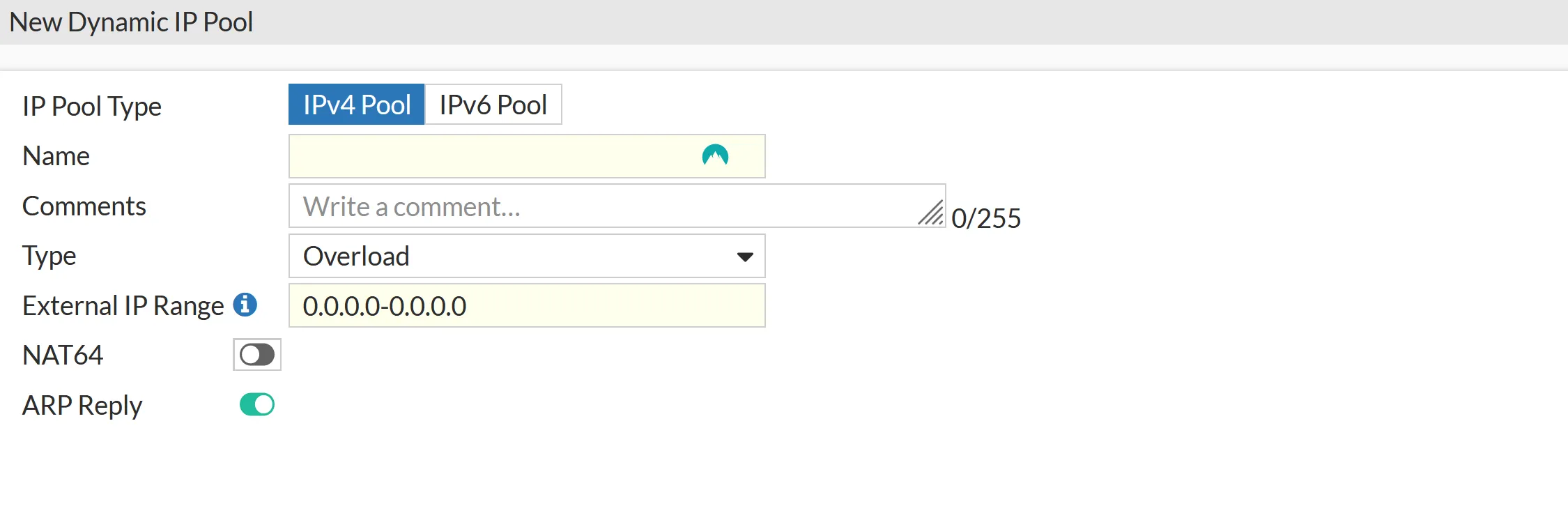
IP Pools
IP Pools in FortiGate are used for dynamic Network Address Translation (NAT) translation for outbound traffic. They allow you to define a pool of public IP addresses that can be dynamically assigned to internal hosts when they initiate outbound connections to external networks. Here’s how IP Pools are commonly used in FortiGate:
- Dynamic Source NAT (SNAT): When internal hosts send traffic to external destinations, FortiGate can dynamically translate their private IP addresses to public IP addresses from the configured IP Pool. This helps preserve private IP addresses within the internal network and allows multiple internal hosts to share public IP addresses for outbound connections.
- Load Balancing: IP Pools can also be used with load balancing configurations. FortiGate can distribute outbound traffic across the available public IP addresses in the pool, helping to distribute the load and optimize network performance evenly.
- Traffic Management and Control: Administrators can implement traffic management and control mechanisms by defining specific NAT policies and rules associated with IP Pools. For example, certain types of traffic or specific internal hosts can be assigned to use specific public IP addresses from the pool, allowing for granular control over outbound traffic flows.
- High Availability and Failover: In high-availability setups where multiple FortiGate devices are deployed in an active-passive or active-active configuration, IP Pools can be synchronized across devices to ensure consistent NAT translation and failover capabilities. This helps maintain continuous network connectivity and seamless failover during device or link failures.
- Security and Policy Enforcement: IP Pools can be integrated with firewall policies and security profiles to enforce security policies on outbound traffic. For example, administrators can define NAT policies to restrict outbound traffic from certain internal hosts to specific public IP addresses in the pool, helping to enforce security policies and prevent unauthorized access.
I would love to get some feedback from you. Was this article helpful? Please share your opinion with me in the comment section below. Or, if you prefer a more personal touch, feel free to email me directly at info@edywerder.ch. Your thoughts and insights are always appreciated.
Before you go …
After diving into the intricacies of configuring NAT on a FortiGate Firewall, you might be interested in expanding your network setup skills further. I recommend checking out this guide on configuring VLANs with Proxmox. It’s a great follow-up for those looking to enhance their virtualized environment, offering practical insights into VLAN setup that complements your newly acquired NAT configuration knowledge. This step-by-step tutorial will ensure you have a robust and efficient network infrastructure in place.
Related Articles
About the author
Hi, I’m Edy Werder. I write hands-on guides about Proxmox, homelab servers, NAS, and WordPress, based on real setups I run and document.
No sponsors, no fluff—just real configs and results.
Enjoying the content?